Zero Trust Managed
Cybersecurity Services
Zero Trust Complete
Zero Trust Complete
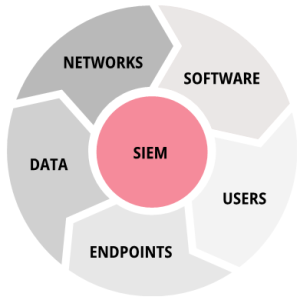
Covers all parts of cybersecurity to ensure better security and full compliance by considering users, endpoints, software, and networks as potential threats until proven otherwise.

Based on the
CISA Zero Trust Maturity Model
Preventing Breaches & Fines
Complying with
Regulators
Authorities
Cyber Insurers
INSURANCE CARRIERS
Enabling Insurance Carriers
to Secure Agencies
• Cyber visibility with dashboards and asset reports
• Security officer support
• Evidence of cyber compliance
• Automated remediation of cyber vulnerabilities at scale
• Vulnerability scans and network penetration testing
AGENCIES
Managing Cybersecurity for
Advisor Firms
• Vulnerability scans and network penetration testing
• Outsourced endpoint and network protection
• Breach response support
• Regulatory and enterprise exam support
• Continual evidence of compliance
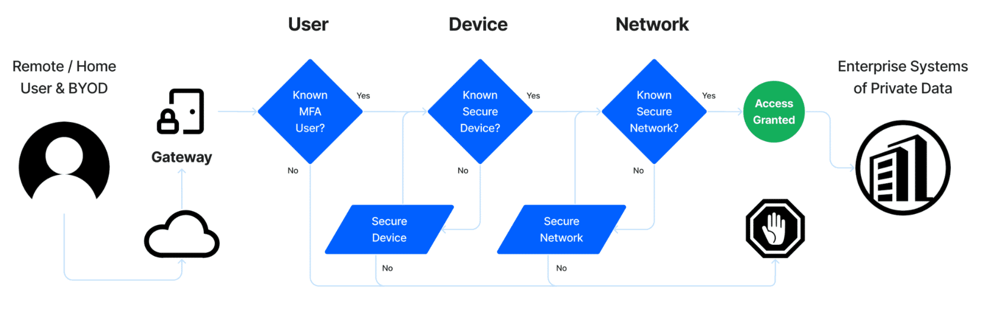
Zero Trust Strategies & Considerations Identity Governance & Administration Privileged Access Management